On April 23, 2026, multiple international cybersecurity agencies jointly released an advisory detailing how China-nexus cyber actors increasingly rely on large-scale covert networks of compromised devices to conduct cyber operations. These networks, mainly composed of vulnerable routers and Internet of Things (IoT) devices, are used to anonymize malicious activity and complicate attribution.
International collaboration on China-linked cyber threats
The advisory was produced by the United Kingdom’s National Cyber Security Centre (NCSC-UK) with contributions from key partners including Australia’s Cyber Security Centre, Canada’s Cyber Centre, Germany’s intelligence and cybersecurity agencies, Japan’s National Cybersecurity Office, the Netherlands’ intelligence services, New Zealand’s National Cyber Security Centre, Spain’s National Cryptologic Centre, Sweden’s National Cyber Security Centre, and several United States agencies such as CISA, FBI, NSA, and the Department of Defense Cyber Crime Center.
Shift in tactics towards covert networks
China-nexus cyber actors have moved from using individually procured infrastructure to exploiting extensive networks of compromised Small Office Home Office (SOHO) routers, IoT devices like webcams and video recorders, and network equipment such as firewalls and Network Attached Storage (NAS) devices. These “covert networks” allow threat actors to mask origin points, maintain deniability, and conduct activities across all stages of the Cyber Kill Chain—from reconnaissance and malware delivery to data exfiltration.
Notable threat groups and networks identified
The advisory highlights specific groups such as Volt Typhoon, which uses covert networks to pre-position offensive cyber capabilities on critical infrastructure, and Flax Typhoon, which employs similar networks for espionage. An example is the Raptor Train botnet, which in 2024 infected more than 200,000 devices worldwide and was connected to the Chinese firm Integrity Technology Group. This company has also been linked by the FBI to Flax Typhoon cyber intrusions.
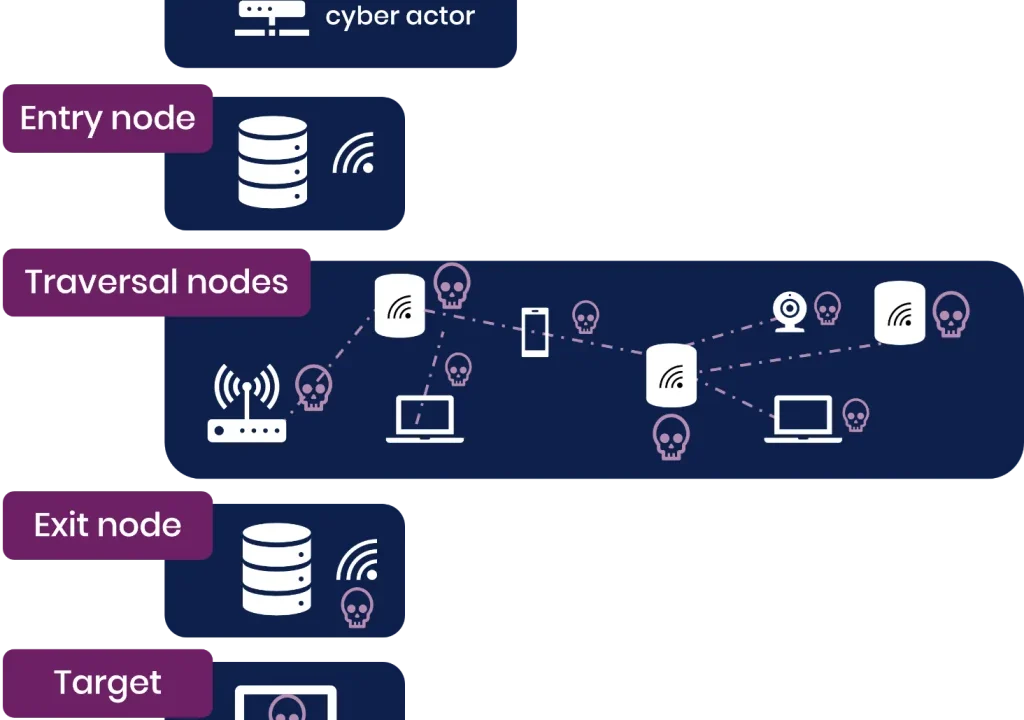
Challenges for defenders and typical network structure
Defending against these covert networks is complicated by their dynamic and large-scale nature. Networks continually evolve as devices are patched, replaced, or newly infected. Consequently, static defense methods such as fixed IP blocklists are largely ineffective. Generally, covert networks function through entry nodes connected by attackers, multiple traversal nodes made up of compromised devices, and exit nodes located near the victim geography, allowing harmful traffic to blend with legitimate internet use.
Recommended defensive measures
The advisory recommends organizations rigorously map and monitor network edge devices, establish baseline connections—particularly to corporate VPNs—and differentiate between expected business traffic and anomalous connections from consumer broadband ranges. Multifactor authentication for remote access is advised universally.
For high-risk or larger organizations, further steps may include implementing IP address allow lists instead of deny lists for VPN connections and applying geographic or profile-based controls on incoming traffic. Smaller entities can utilize free resources such as the NCSC Cyber Action Toolkit to enhance defenses.
Why it matters
This advisory underscores the increasing sophistication and scale of China-nexus cyber campaigns that exploit everyday consumer and enterprise devices to create vast covert networks. These botnets facilitate stealthy cyber intrusions and espionage affecting critical infrastructure and sensitive information globally. Understanding and mitigating these threats is vital for organizations to maintain cybersecurity resilience amid evolving tactics.
Read more Cybersecurity stories on Goka World News.
Sources
This article is based on reporting and publicly available information from the following source: